Let’s cut to the chase—ransomware isn’t going away. If anything, it’s mutating, growing teeth, and hunting for your weakest link.
Businesses that think they’re too small, too niche, or too careful to be a target? Think again. The cyber threat landscape is getting nastier by the minute, and attackers are not playing fair.
Forget the Movies—Real Cyberattacks Are Messy
There’s no clean “mission complete” moment. Real-world ransomware attacks are chaotic, unpredictable, and ruthless.
Cybercriminals don’t follow a script—they pivot fast, test different tactics, and look for cracks in your defenses while you’re sipping your morning coffee.
According to data from Barracuda’s Managed XDR, ransomware attacks have quadrupled in 2024. That’s not a typo. Four times more threats, many powered by the ever-evolving beast known as Ransomware-as-a-Service (RaaS).
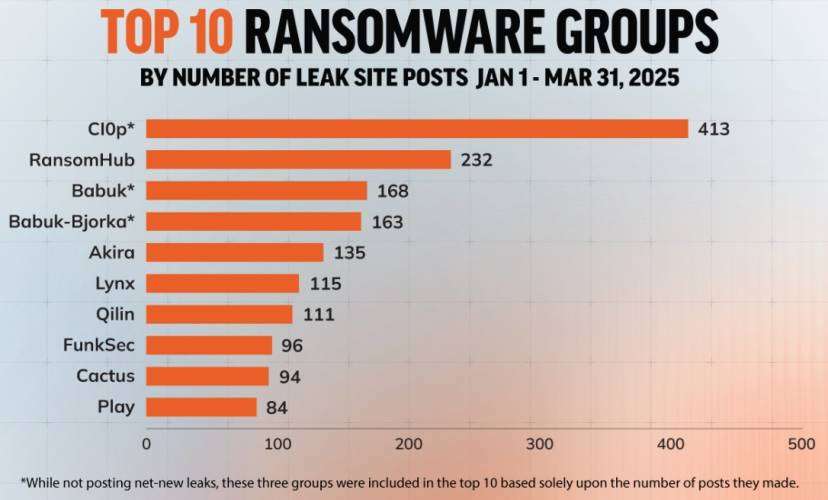
These RaaS groups—think Akira, RansomHub and their gang—are making it dangerously easy for even low-skilled hackers to launch full-scale attacks. It’s like giving kids the keys to a Formula 1 car. The tools are powerful, polished, and built to break in.
Ransomware is Now a Team Sport
Modern attacks aren’t just a quick file drop and boom—you’re locked out. They’re multi-stage, multi-prong invasions. Attackers don’t knock once and walk away. They linger, adapt, and exploit whatever blind spot they find.
In one attack, crooks slipped into an exposed server and in just 74 minutes, they elevated their privileges and detonated Akira ransomware. That’s just over an hour. No coffee break, no warning. Just boom.
Another case? Hackers waltzed in through a forgotten “ghost” contractor account left active on a VPN—no MFA, wide open. They roamed around, escalated to admin rights, and tried to deploy ransomware.
Lucky for the company, they tripped a wire on a protected device and got shut down. But if those protections weren’t in place? It would’ve been game over.
What’s the Lesson? Security Gaps = Open Invitations
Hackers don’t need an engraved invite—just a sliver of opportunity. A stale password. An inactive account. A missing MFA setup. They’ll find it, use it, and leave you holding the ransom note.
How Do You Fight Back? Layer Up Like It’s Winter in Antarctica
The only real answer to this chaos is layered, integrated security. One tool isn’t enough. You need a full orchestra—network, server, cloud, email, endpoints—all singing the same security tune.
Here’s your non-negotiable checklist:
- MFA Everywhere: Especially on VPNs. If your login screen doesn’t stop a basic brute-force attempt, you’re a sitting duck.
- Password Hygiene: Change them. Often. Especially admin-level ones. Stale passwords are hacker gold.
- Audit All Active Accounts: If it’s not in use, shut it down. Least-privilege access should be the rule, not the exception.
- Get Full Visibility: You can’t protect what you can’t see. Go with a platform approach. Extended Detection and Response (XDR) ties everything together and makes sure your security team sees the full picture.
XDR = Eyes on Everything
With a strong XDR platform, your team can see every corner of the digital estate—from inboxes and endpoints to shady cloud activity. It shrinks the window of opportunity for attackers and increases the chance of stopping an attack before it spirals out of control.
Ransomware Surge Shows No Signs of Slowing, Reports Reveal
According to Verizon’s “2024 Data Breach Investigations Report,” released in May of last year, ransomware and data extortion accounted for 32% of all reported cyberattacks.
Alarmingly, 92% of industries identified ransomware as a top cybersecurity threat, underscoring the universal nature of the risk.
Supporting those findings, Sophos’ “State of Ransomware 2024” report revealed that 59% of organisations were affected by ransomware in 2024, a figure that experts warn could continue climbing as hackers adopt more aggressive tactics and target wider sectors.
The diversity of ransomware strains is also expanding. In 2024 alone, cyber threat intelligence firm Intel471 documented 101 different ransomware variants, including ominously named strains such as FSOCIETY, Funksec, GovRansomArtist, HellCat, and Mad Liberator.
The variants reflect not just creativity in branding but also significant differences in encryption techniques, distribution methods, and extortion strategies.
The start of 2025 has already seen a sharp rise in ransomware incidents. In the first five weeks of the year, U.S. ransomware attacks jumped 149% year over year. 378 incidents were reported, compared to just 152 in the same period in 2024.
With damages from ransomware projected to reach $30 billion annually by 2030, industry leaders warn that organisations need to start shifting from reactive measures to proactive, holistic defenses—or risk becoming the next headline.
New Ransomware Groups Active Since 2025
Several new ransomware groups (11) have emerged since the start of 2025, signaling a continued expansion of the cybercriminal landscape.
Among the newly active threat actors are Ailock, Belsen Group, CrazyHunter, Cs-137, D0Glun, GD LockerSec, Linkc, NightSpire, Ox Thief, Run Some Wares, SECP0, Sonshi, and VanHelsing—each bringing its own tactics and targets
Notable trends
In February 2025, a leak of internal chat logs from the notorious ransomware group Black Basta gave the cybersecurity world an unfiltered glimpse into the inner workings of one of the most elusive cybercrime outfits to date.
The logs didn’t just reveal internal bickering and strategic planning—they confirmed a troubling trend many experts had long suspected: ransomware groups are reinvesting their earnings into zero-day exploits.
For months, security analysts speculated that criminal organizations were funneling ransom payments into black-market tech tools. But the Black Basta logs turned suspicion into certainty.
On November 23, 2023, a conversation within the group discussed the potential purchase of a zero-day exploit targeting Ivanti Connect Secure. The asking price? $200,000—a steep sum, even in the cybercrime world.
The exploit was advertised as an unauthenticated remote code execution (RCE) flaw, based on an unknown memory corruption vulnerability.
Now, to be clear, it’s unknown whether the group ever made the purchase. But the detail and seriousness of the conversation suggest that the offer was under real consideration.
Analysts have tried to link the exploit to known Ivanti vulnerabilities disclosed around that time—CVE-2023-46805, CVE-2024-21887, and CVE-2024-21893—but none match the characteristics of the exploit described in the chats.
The closest fit may be CVE-2025-0282, another Ivanti flaw that does involve memory corruption, but discrepancies in affected versions suggest the mystery zero-day may still be unpatched—and still in use.
Even more revealing? Black Basta did go through with another high-stakes purchase: a Juniper firewall exploit.
According to the logs, the group compared a known, authenticated RCE exploit—which offered limited user-level access—with the version they bought. The paid version granted full root access, giving them a dangerous level of control over targeted systems.
The leak also hinted at a sudden halt in Black Basta’s public activity—the last update on their leak site was January 11, 2025—raising questions about whether the group has gone dark, rebranded, or shifted strategies.
Still, the broader implications are clear: ransomware groups are no longer just demanding payouts—they’re investing like tech startups, acquiring powerful tools to stay ahead of defenders.
From Ransomware to Extortionware: How Cybercriminal Tactics Are Evolving
Cyberattacks may appear chaotic from the outside, but many ransomware groups follow a well-established sequence: initial access, reconnaissance, credential theft, lateral movement, data exfiltration, and finally, file encryption.
It’s a familiar script, and one that defenders have learned to anticipate. But in recent years, some cybercriminals have begun to deviate from the norm.
Increasingly, threat actors are choosing to bypass the encryption step entirely. Instead of locking files and demanding payment for decryption, they gain access through unsecured VPNs or Remote Desktop Protocol (RDP) and move straight to stealing sensitive data.
Once they have it, they threaten to leak it unless a ransom is paid. This approach, known as extortionware, is often quicker, quieter, and harder to trace.
Other groups, such as the well-known LockBit gang, are adopting what’s known as “Living off the Land” tactics.
Rather than deploying malware that might trigger alarms, they use legitimate tools already present in a target’s environment—things like PowerShell, Windows Management Instrumentation (WMI), and remote management software.
Full-spectrum security isn’t overkill — it’s survival.
It’s the difference between a minor inconvenience and a business-ending crisis. In a world where attackers are smarter, faster, and more relentless, your defense needs to be just as advanced, and just as comprehensive.
Because in 2025, the difference between a ransomware horror story and a near miss isn’t luck—it’s visibility, speed, and tight security.











